IEEE 802.11 Frames and How to Get Them
In the next months we will present some insights we got while analyzing devices that provide so-called industrial Wireless LAN. To get a general understanding of these devices some basic knowledge about Wi-Fi and the corresponding standards is vital. This post will provide an overview of the main properties of the 802.11 standard and will explain what kind of frames one can expect to see.
What is IEEE 802.11 anyway?
The first Wi-Fi standard was published by the IEEE in 1997, the 802.11 standard. Since then many improvements were made and the original standard has been superseded long time ago (see here for a timeline). The standard proposes a way to communicate wirelessly in a similar manner like other IEEE 802 standards, e.g. like the 802.3 did for wired Ethernet connections. Generally the most important objective of these standards is the management of the physical medium in use – in this case the air.
The air as a shared medium
Any communication system needs a medium to send signals through, e.g. the cable in the case of wired communication. Such medium is often restricted in its use in the way that only one party can send signals at a time. If two entities are emitting signals simoultaneously on the same medium they might disturb each other. This kind of communication systems are called half-duplex. One way to handle this problem is a mechanism in which the participants of a medium are cooperating to only send data while the medium is free to use.
Managing simultaneous communication is necessary for wired and wireless communication. However, the main challenge for latter is its transportation medium – the air. Since it is difficult to restrict its access, it is way more difficult to restrict and manage the corresponding communication. In contrast, access to a cable is easier limited to a few specific participants.
For wireless communication participants will send with different signal strength. As a consequence packets might get lost. This is seldom the case for wired communication. Another issue in wireless communication is that not all participants are aware of each other. If two of them are sending messages over the air without knowing each other they are unable to cooperate. This phenomenon is called "hidden node problem" and is illustrated below. If node A and C send data simultaneously to B, B might receive scrambled data. This can be prevented more easily in wired networks. Here typically everyone can listen to the medium and thus can cooperate more easily.
How to analyze 802.11 frames
To actually analyze 802.11 frames one needs to know how to capture them properly. This section provides some basic knowledge about sniffing Wi-Fi frames. You may use different tools and you may need to adapt these tips to your system environment.
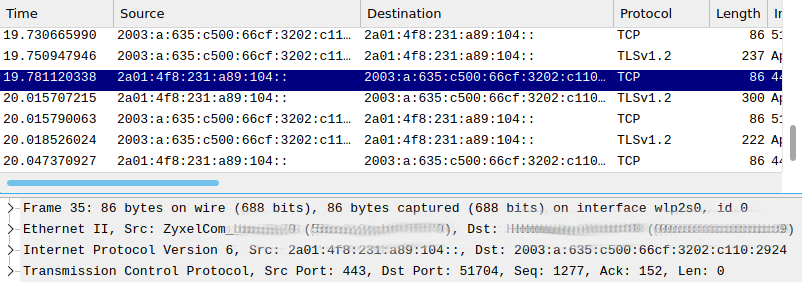
If you open a network protocol analyzer to capture the data arriving at your wireless card you will only see frames which look very similar to those you would see on your Ethernet card. And indeed they are the same. Furthermore, you will not see any packets of clients nearby. So the question arises where you can see the actual 802.11 frames? And why can't you see the data of other machines? The packets you are seeing in this case are the ones that the wireless card already has decoded. These packets are the payload of the actual Wi-Fi frame. Likewise, corresponding results in Ethernet interfaces will not include the 802.3 part of the Physical and Data Link Layer either. Below you can see a Screenshot of such capture attempt with Wireshark.
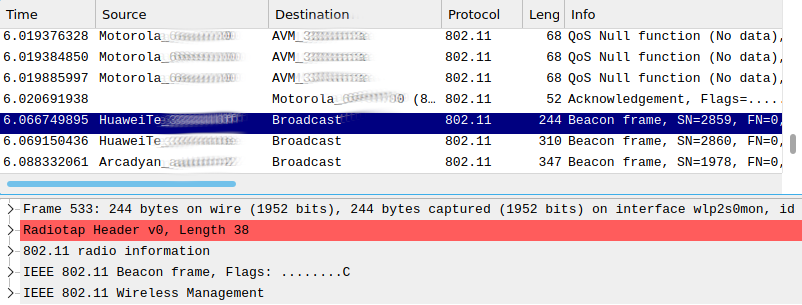
If you really want to see all the 802.11 magic you need to capture the traffic while the wireless card is set to monitor mode. In this mode you are able to see the actual 802.11 frames that were sent and seen in the air instead of the already parsed ones. Furthermore, you can observe all packets in the air, not only those sent to your machine.

Unfortunately, not all wireless cards are able to use the monitor mode. One way to check whether your Wi-Fi card is able to do so is with the tool airmon-ng. Here you can easily enable the mode on your card, too.
[user@machine ~]$ sudo airmon-ng check wlan0
Found 2 processes that could cause trouble.
Kill them using 'airmon-ng check kill' before putting
the card in monitor mode, they will interfere by changing channels
and sometimes putting the interface back in managed mode
PID Name
602 NetworkManager
696 wpa_supplicant
[user@machine ~]$ sudo systemctl stop NetworkManager.service wpa_supplicant.service
[user@machine ~]$ sudo airmon-ng start wlan0
PHY Interface Driver Chipset
phy0 wlan0 ath9k Qualcomm Atheros AR9462 Wireless Network Adapter (rev 01)
(mac80211 monitor mode vif enabled for [phy0]wlan0 on [phy0]wlan0mon)
(mac80211 station mode vif disabled for [phy0]wlan0)Once you have the monitor mode activated, you can see the frames that are defined by the 802.11 standard.
In the next section we will go into more detail about the functions of the different frames and what they are used for.
802.11 Frames
There are basically three frame types defined in the IEEE 802.11 standard: Data, Management and Control frame. Every frame consists of a Media Access Control (MAC) header, a frame body and a Frame Check Sequence (FCS) to ensure basic integrity of the frame via the CRC-32 algorithm. The frame body can be encrypted (e.g. if WPA2 is used) and is of variable size. The general MAC frame format is seen in the figure below (as seen in 802.11 standard 802.11-2016, p. 638).
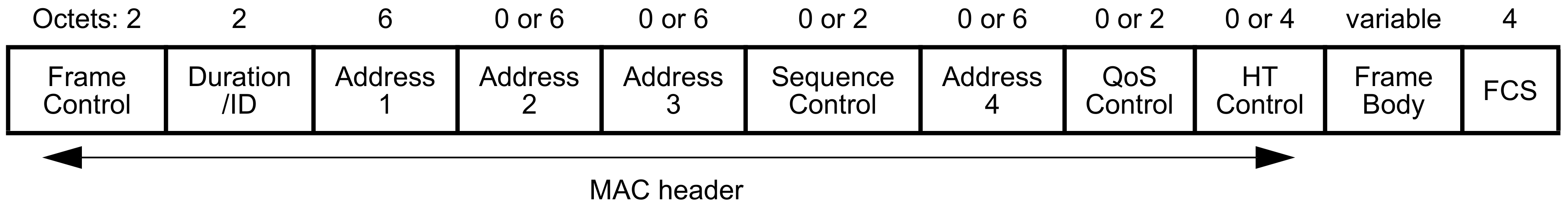
Data frames contain the actual data as payload, e.g. an Ethernet frame. The content can not be accessed if there is an encryption method like WPA2 in use. It is not trivial to attack a properly configured encrypted connection as long as there is no known weakness in the encryption scheme. On the other hand, if no encryption is in use one can easily read the data by capturing Data frames.
Management frames are needed to establish and manage the communication between participants. Some examples of Management frames are Authentication frames, Association frames, Probe Requests and Beacon frames. The latter are some form of "advertisement". Beacon frames are used by Access Points (APs) to publish basic information about the APs' capabilities. As a consequence, nearby clients find neccessary information about their surrounding APs. This enables them to decide to whom they want to connect to. The following picture shows a typical Beacon frame and its information provided.

As you can see the Beacon frame contains many details necessary for the management of the wireless medium e.g. the SSID of the AP, the frequency of the channel it is sending, the regulatory country information and so on. This information will never be displayed when capturing in the management mode of the card (see above), but is important if you want to manipulate the wireless communication.
Control frames are used to control the packet flow. An important example of this type of 802.11 frames are the Request To Send (RTS) and Clear To Send (CTS) frames. These are used to explicitly block the medium so that challenges like the hidden node problem (see above) can be tackled. A station might send an RTS frame to announce its intention to use the medium for a specific time. A client may respond with CTS frames. They acknowledge a station's request and propagate it to nearby clients. This way, even clients that are out of reach of the RTS Frames get the corresponding information. Every node receiving CTS frames shall stop sending data. Consequently, the requesting station is free to send data. The following image illustrates an RTS frame.

The frame contains the information about the transmitter address (the station that wants to block the medium) and the receiver address. Furthermore, it contains a duration field to announce how long the medium shall be blocked.
The next blog post will contain more information about typical attacks on Wi-Fi networks. It is important to have a general understanding of 802.11 frames and their specific usage to understand the attacks described there. Therefore, it is recommended to familiarize yourself with the different frame types a bit.
Further Reading
- Current 802.11 standard 802.11-2016
- Mathew Gast, 802.11 Wireless Networks: The Definitive Guide, O’Reilly, 2005.
