A Starter Guide to Encryption and Fingerprinting
From time to time we are asked what the deal is with the 'Fingerprints' and the 'Keys' in our contact details. Now, I want to give you an explanation :) In order to do so, I am trying to give you a very brief overview about mail encryption, in which keys and fingerprints are generally used. But first of all, I want to point out, that this post does not address a technical audience. Instead, I want to write to non-technical persons like managers, project leaders, moms, dads and grand parents. As a consequence, I will ignore any mathematics and solely concentrate on the bare concept of mail encryption. In the beginning, I will talk about goals and reasons of encryption. Afterwards I explain the basics of symmetric and asymmetric encryption. This leads to PGP and the usage of fingerprints. If questions arise, please do not hesitate to ask us (writing encrypted mail would be best).
Goals of encryption
Encryption is used to prevent others from reading your data or communication. Only those intended to read the data, should be able to do so. At this point one argument very often arises: Why should anybody want to read my messages? There is nothing of importance in my communication and I have nothing to hide. We usually answer with a question: Can you please send us all your texts, mails and bank credentials (or maybe your health records)? Most people would not do so. Because it is not about hiding something, it is about making sure of your privacy. With this being the motivation, there are several goals secure communication shall satisfy:
- access to the message only for the intended recipient(s)
- identification of the expected sender
- easy exchange of encryption keys
- few effort for encrypting
Encryption and Pretty Good Privacy
With those goals at hand, let's have a look on the different types of encryption. There are basically three types of encryption: symmetric encryption using one key for encryption and decryption, asymmetric encryption which uses a different key for encryption and decryption and there is a hybrid encryption, that uses both.
One secret key
In traditional encryption both sides use the same key for encryption and decryption. This way of encryption is called symmetric encryption because the both sides have mirroring conditions. Here is an example to understand the terminology:
Frank and Paula are in school and they intent to write secret paper messages to each other, which the teacher or class-mates should not read in case of interception. They agreed on swapping letters with numbers. This procedure is the encryption algorithm. Additionally, they secretly decided which number corresponds to which letter. This is their encryption key. Now they are able to cipher and decipher messages, they exchange. This is called a symmetric encryption, since both need to know the corresponding numbers in order to encrypt/decrypt correctly. In effect, an eavesdropper cannot read their messages without knowing the key. So the more complex the key is, the more secure the encryption becomes.
Symmetric encryption has one big disadvantage: every participant of the communication needs to know the same key. So if one participant 'loses' it or shares it with the wrong person, all secrecy is lost - as it was the case with the Enigma machine. Additionally, after 'losing' the key a new one has to be generated and exchanged. In fact, the key exchange is a big issue (even in science). Exchanging symmetric keys demands a secure way of communicating, which is easy, if you meet in class everyday, but which gets more difficult in case of big distances. Another aspect is identification. Using symmetric cryptography makes it hard to identify the sender of the message, since everyone has the same key. Though, signing a message via symmetric cryptography is a problem. The following image gives a visualisation of the concept of symmetric encryption.

Private and public keys
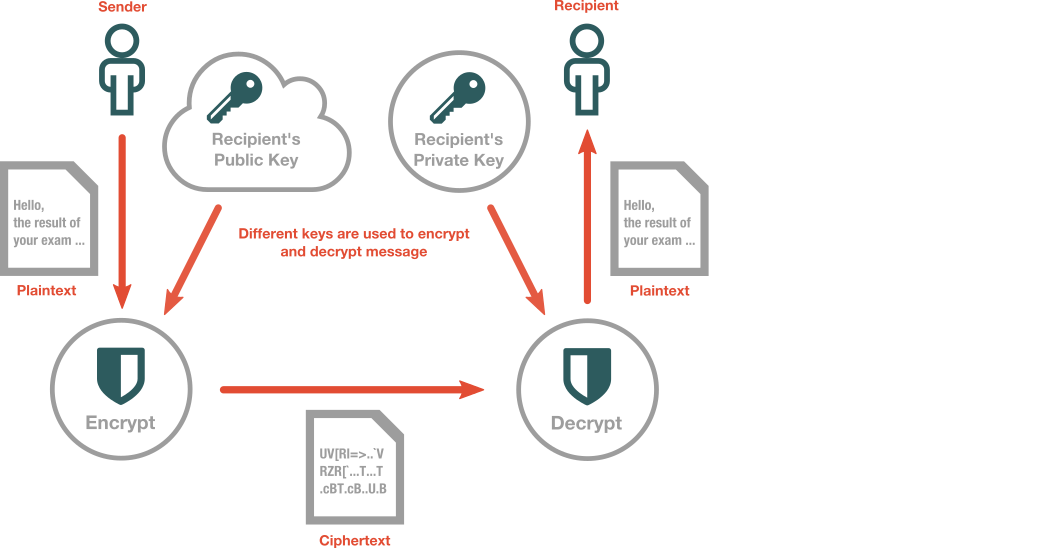
This problem was solved with the introduction of asymmetric encryption. In its simplest form every participant of the communication has one key pair, consisting of a private key, which is only known by the addressee, and a public key, which is known by everyone. The keys are generated together and have a mathematical relationship. In asymmetric mail encryption messages are encrypted using the recipient's public key and deciphered by the recipient's private key. Note the difference to symmetric encryption, where both is done with one and the same key. One big feature of this approach is, that it allows an easy implementation of signatures in order to verify a message's sender. Digital signatures are basically done in the reverse way of encrypting mails. Here, the sender uses its private key for signing and the recipient uses the sender's public key for verification of the signature. Many people publish publicly their keys on servers, so they are easily accessible. This allows everyone to verify mails of them or to send them encrypted messages. Keys not published on keyservers can easily be exchanged via mail. The contrary goes for private keys. Private keys should not be shared, as the name denotes. So, keep them secret! The following graphic should highlight the concept.
So all the theory is quite unexciting without having any practical implemenation. One of the first implementations was Pretty Good Privacy (PGP) by Phil Zimmerman. PGP handles all the math and algorithms, so you don't have to bother. Unfortunately, there was a big internal discussion about licenses and patents, which lead to a new standard, namely OpenPGP. Today a widely used application for implementing this standard is the Gnu Privacy Guard (GPG/GnuPG). It's open source and free, so everybody is able to have a look at the source code and to share it.
Fingerprints
So back to the intial question, which also covered fingerprints. Every key that is generated is unique. This is crucial, otherwise a second key might enable strangers to encrypt your mails. As a consequence, every key has a so called fingerprint, which is a unique string, that identifies the key. Basically like the fingeprint of a person's thumb. Now, if one is interested in communicating with someone, it's recommended to check, whether the fingerprint which the addressee publicly announces, is identical to the public key, one uses for encryption. This is like checking the identity card before talking to someone. This ensures that only the person who is the real addressee, is able to encrypt the message, since he owns the corresponding key. For that reason we announce all of our key's fingerprints on our about page.
Conclusion
Encryption is a very complex, yet important topic. We hope to have shown an easy explanation of the basic theory of encryption. The practical part was intentionally left open. We will cover a simple way of using the PGP/GPG encryption in an upcoming blog post.
Further Reading
- WP: one-way functions
- Official site of the open PGP project: How PGP works
- Cryptography and Data Security, Dorothy Denning & Elizabeth Robling, 1982
- Introduction to modern cryptography, Jonathan Katz & Yehuda Lindell, 2007
- Paper of C. d. Roza on math in asymmetric cryptography (SANS Institute): "Mathematical Underpinnings of Asymmetric Cryptography"
- Lecture "Introdution to Modern Cryptography" by M. Bellare and P. Rogaway (UCSanDiego): Overview and notes on Symmetric Encryption
